Cisco ISR 4431 Setup and Troubleshooting Guide
A comprehensive HOWTO for configuring, securing, and maintaining the Cisco ISR 4431 router. Learn initial setup, VLANs, VPN, NAT, QoS, firmware updates, and practical troubleshooting.
This guide walks you through the setup and optimization of the cisco isr 4431 router for reliable small-business networking. You’ll learn essential initial configuration, security hardening, firmware maintenance, and practical troubleshooting steps. By following these steps, homeowners and tech enthusiasts can improve stability, performance, and security of their edge router, including NAT, VPN, and QoS basics.
What is the cisco isr 4431 and who should use it
The cisco isr 4431 is a high-performance edge router designed for small-to-medium businesses and advanced home labs. It combines routing, security, and WAN connectivity in a single chassis, making it a versatile choice for sites with growing bandwidth needs. The WiFi Router Help team notes that this model targets professionals who want robust features without jumping to a full enterprise firewall. In practice, users deploy the 4431 to handle Internet access for several LAN segments, protect traffic with integrated firewall capabilities, and support VPN tunnels for remote workers. If you’re evaluating options, compare this device to other ISR 4000-series models to gauge performance, scalability, and feature sets. For many households and small offices, the 4431 provides a practical balance between flexibility and manageability. In this guide we’ll cover setup, hardening, and troubleshooting so you can deploy it with confidence and clarity, even if you’re stepping up from a consumer-grade router. According to WiFi Router Help, the device is well-suited for environments that require solid security, reliable Wi-Fi integration, and scalable routing.
Basic setup: initial access and secure credentials
Begin by connecting to the device console using a serial cable or USB console adapter. Power on the unit and access the CLI through the console. Set a strong hostname and domain name, then configure secure management credentials (enable secret) and enable password-encryption to protect stored secrets. Enable SSH (ip ssh version 2) and disable Telnet to reduce exposure. Create an admin user and restrict VTY access with access-class rules if available. Generate a strong RSA key pair for SSH (crypto key generate rsa) and ensure the key size is adequate (e.g., 2048 bits). Save the running configuration to startup configuration (write memory or copy running-config startup-config). This ensures you can manage the device securely from day one. WiFi Router Help emphasizes securing management access early to minimize attack surface and ensure reliable remote administration.
Network segmentation and QoS basics
Plan your network into logical segments using VLANs to isolate traffic types (e.g., management, voice, data). Assign interfaces to the appropriate VLANs and enable inter-VLAN routing if the device will act as a gateway. QoS helps prioritize latency-sensitive traffic such as VoIP or video conferencing, ensuring stable performance even under load. Start with simple policies: classify traffic by source/destination IP ranges or port numbers, set higher priority for voice/video, and throttle non-critical traffic when needed. Document your VLAN IDs and QoS rules so teammates can reproduce the configuration. This approach improves reliability for mixed workloads and reduces jitter. As you implement, test with representative traffic to verify that priority paths function as expected while guest or IoT networks remain segmented.
Security hardening and VPN options
Hardening begins with least-privilege access: disable unused services, enforce SSH only, and implement strong authentication. Create ACLs to filter inbound traffic from untrusted networks and restrict management access to trusted subnets. The ISR 4431 supports site-to-site VPNs and remote access VPNs; configure IPsec or SSL VPNs to secure connections for remote workers. When designing VPNs, prefer modern cipher suites and regularly rotate pre-shared keys or use certificates where possible. WiFi Router Help notes that a robust security posture also includes periodic firmware checks and monitoring for anomalous activity, which helps reduce the risk of credential compromise or exploit attempts.
Management, monitoring, and common troubleshooting tips
Regular monitoring helps you catch issues early. Use commands like show ip interface brief, show version, show running-config, and show logging to verify status and identify misconfigurations. If a WAN outage occurs, verify physical links, interface status, and DNS settings. Keep a change log and back up configurations frequently so you can rollback quickly if something breaks. When troubleshooting, reproduce issues in a controlled maintenance window and test one variable at a time. This disciplined approach reduces guesswork and speeds restoration of service. According to WiFi Router Help, maintaining a clear audit trail makes it easier to troubleshoot correlated events over time.
NAT, routing, and firewall configurations
Configure NAT to provide Internet access to internal networks, typically by marking inside and outside interfaces and defining NAT rules. Ensure the inside interfaces connect to your internal networks and the outside interface faces the Internet. Basic firewall rules should protect inbound traffic while allowing essential services. For example, create an ACL that blocks unsolicited inbound traffic from the Internet to internal devices unless explicitly allowed. This section also covers basic static routes or dynamic routing as needed for multi-homed setups. Keep changes incremental and validate each step with tests from a management workstation.
Firmware updates and maintenance practices
Develop a maintenance cadence that aligns with your network needs. Check for firmware updates from Cisco and apply them in a controlled maintenance window after validating compatibility with your existing configurations and hardware. Before applying updates, export a complete backup of the startup-config and running-config. Review release notes for potential breaking changes and feature deprecations. After updating, verify that all services (VPNs, QoS, firewall rules) continue to function as expected and monitor for any unusual behavior during the first 24–48 hours.
Save, verify, and document changes
Always commit changes to startup-config and verify their persistence across reboots. Use commands like show running-config and show startup-config to compare. Maintain a centralized change log and document each modification with the rationale, date, and person responsible. Documentation should include network topology, VLANs, IP addressing, and firewall/NAT rules. This practice simplifies future troubleshooting, audits, and upgrades, and supports smoother handoffs between admins.
Authority sources
For deeper study and validation, consult trusted sources such as Cisco’s official ISR documentation, NIST security guidelines, and CISA best practices. These references provide authoritative context for best practices in router configuration, security hardening, and incident response. You will often find step-by-step examples, command references, and security recommendations that complement this guide.
Tools & Materials
- Laptop or admin workstation with terminal/emulation(Windows: PuTTY/Tera Term; macOS/Linux: Terminal; ensure SSH client is installed)
- Console cable (RJ-45 to DB-9 or USB-to-Serial adapter)(Needed for initial access via the console port)
- Ethernet cables (Cat6 or better)(For connecting the ISR to LAN/upstream gear)
- Power supply and UPS(Optional but recommended for stable maintenance windows)
- Administrative passwords and credentials(Include strong enable secret, SSH keys, and VPN credentials if applicable)
- Access to Cisco support portal or documentation(Helpful for firmware notes and feature guidance)
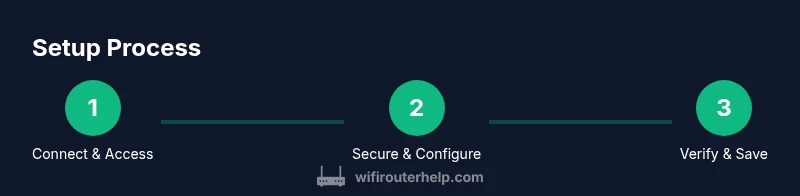
Steps
Estimated time: 2-3 hours
- 1
Gather prerequisites
Assemble all required hardware and credentials before touching the ISR 4431. This minimizes mid-task interruptions and reduces configuration errors. Confirm you have console access, network plans, and a plan for secure credentials.
Tip: Document device serial numbers and initial passwords in a secure vault. - 2
Connect to the console and boot
Attach the console cable, power on the router, and access the CLI from your workstation. Verify you can reach the device prompt and note the initial boot messages for any hardware alerts.
Tip: If you don’t see a prompt, verify the console adapter speed and cable integrity. - 3
Set basic security credentials
Enter global configuration mode and set hostname, domain, and secure admin credentials. Enable SSH v2, disable Telnet, configure password encryption, and generate an RSA key pair for SSH access.
Tip: Use a password manager to generate a strong, unique password; never reuse credentials. - 4
Configure internal and external interfaces
Assign IP addressing to LAN and WAN interfaces or enable DHCP as appropriate. Mark the inside interface for internal traffic and the outside interface for Internet-bound traffic. Verify interfaces come up with appropriate IPs.
Tip: Double-check interface descriptions to avoid routing mistakes later. - 5
Implement VLANs and QoS basics
Create VLANs for management, data, and voice if needed; assign interfaces accordingly. Establish simple QoS rules to prioritize voice/video and limit non-essential traffic during peak periods.
Tip: Document VLAN IDs and QoS priorities for future audits. - 6
Enable NAT and firewall basics
Configure NAT rules so internal devices access the Internet. Set basic firewall rules to block unsolicited inbound traffic, and allow only necessary services. Validate with a controlled test from an internal host.
Tip: Start with conservative rules and expand as you confirm operation. - 7
Configure VPN options (if required)
If remote access or site-to-site VPN is needed, scaffold IPsec or SSL VPN settings with minimal exposure. Use certificates where possible and rotate cryptographic keys on a schedule.
Tip: Test VPN connectivity during a maintenance window before enabling in production. - 8
Save, verify, and document
Store the configuration to startup-config and verify persistence after reboots. Update the network diagram and change logs with reasoning and dates.
Tip: Keep a copy of the running and startup configs off-device as a safety measure.
People Also Ask
What is the best use case for the Cisco ISR 4431?
The cisco isr 4431 is well-suited for small-to-medium businesses that need robust routing, integrated security, and site-to-site VPN capabilities in a compact form. It supports multiple VLANs, QoS, and scalable WAN options for growing networks.
The 4431 is great for SMBs needing strong routing and security in one device.
Can I configure VPNs on the ISR 4431?
Yes. The ISR 4431 supports IPsec and SSL VPN configurations for remote workers or branch-to-branch connections. Plan your VPN topology carefully and ensure you have the necessary credentials or certificates.
VPNs are supported; configure IPsec or SSL VPN as needed.
How do I reset the router to factory defaults?
Factory reset typically involves holding a reset button while powering on to restore default settings, followed by re-entry of a fresh configuration. After reset, reconfigure security settings, interfaces, and VPN as needed.
Factory reset restores defaults; you’ll need to reconfigure from scratch.
Is SSH required for secure management?
SSH is strongly recommended for secure remote management. Disable Telnet, enable SSH, and use strong key pairs to prevent credential interception.
Yes—use SSH for secure remote management.
Where can I find firmware updates and support?
Firmware updates and official guidance are available from Cisco’s support portal. This ensures compatibility with your model and access to security fixes and feature enhancements.
Check Cisco's support portal for updates and guides.
What are common troubleshooting steps?
Verify physical connections, review interface statuses, check running-config vs startup-config, and inspect logs for errors. Reproduce issues in a controlled manner to isolate root causes.
Check cables, interface status, and logs; reproduce issues carefully.
Watch Video
What to Remember
- Plan VLANs and security before touching a device.
- Secure management access from day one (SSH, not Telnet).
- Document changes and back up configurations regularly.
- Test changes in a controlled window and monitor after updates.